For attorneys, anonymous online accounts can present serious challenges. Whether it’s a burner social media profile spreading defamatory claims, a blog smearing a client, or a shadowy post tied to ongoing litigation, the central question is always the same: Who is really behind it? That’s where unmasking anonymous accounts comes into play, and it’s an area where private investigators specializing in OSINT (open-source intelligence) can add real value.
To be clear, we’re not talking about anything illicit here. There’s no cloak-and-dagger hacking stuff that’ll land you in hot water. Unmasking an anonymous account requires patience, a solid methodology, and the uncanny ability to connect the dots across the vast—often wild—open web.
How to Start Tracking an Anonymous Account by Using OSINT
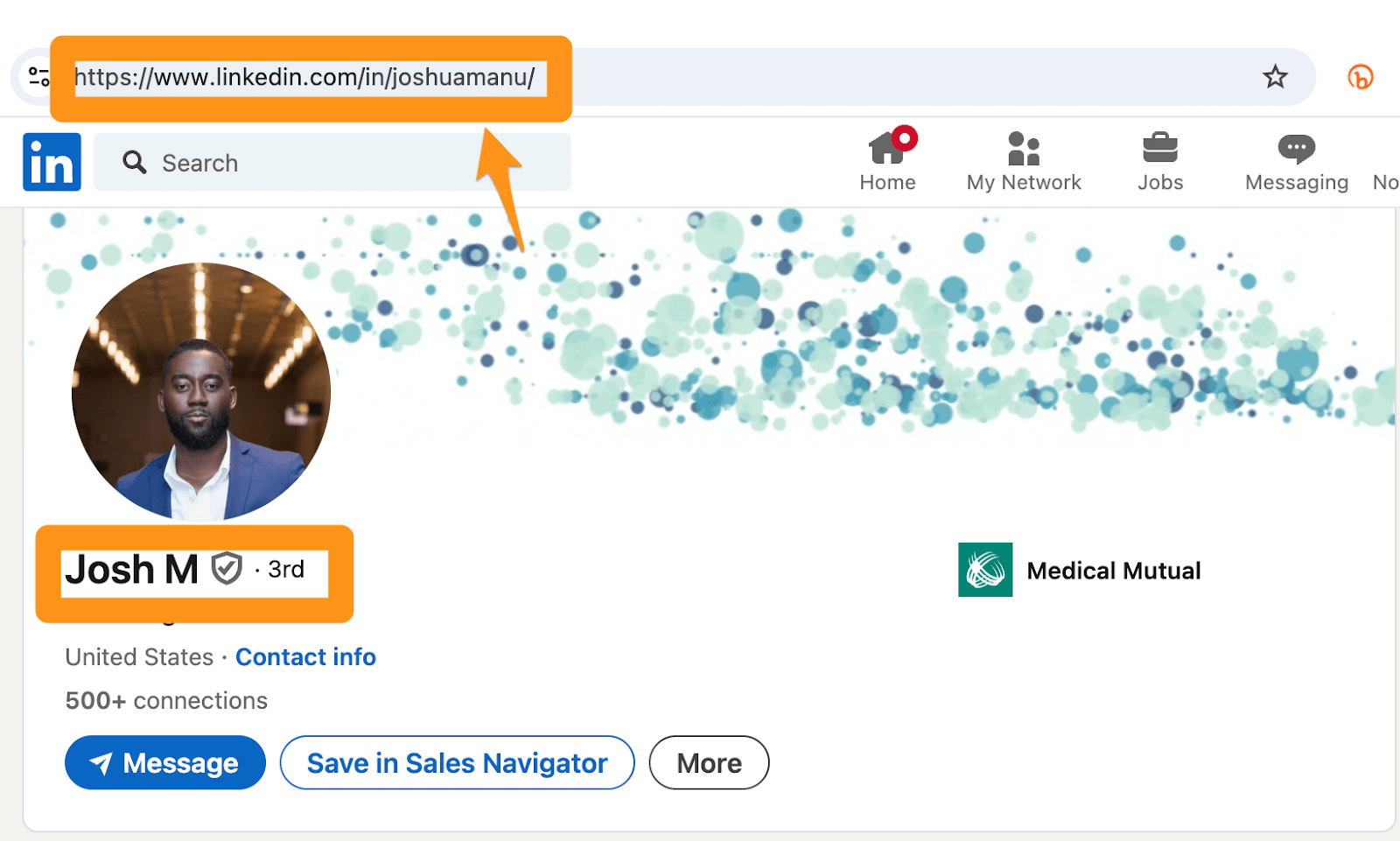
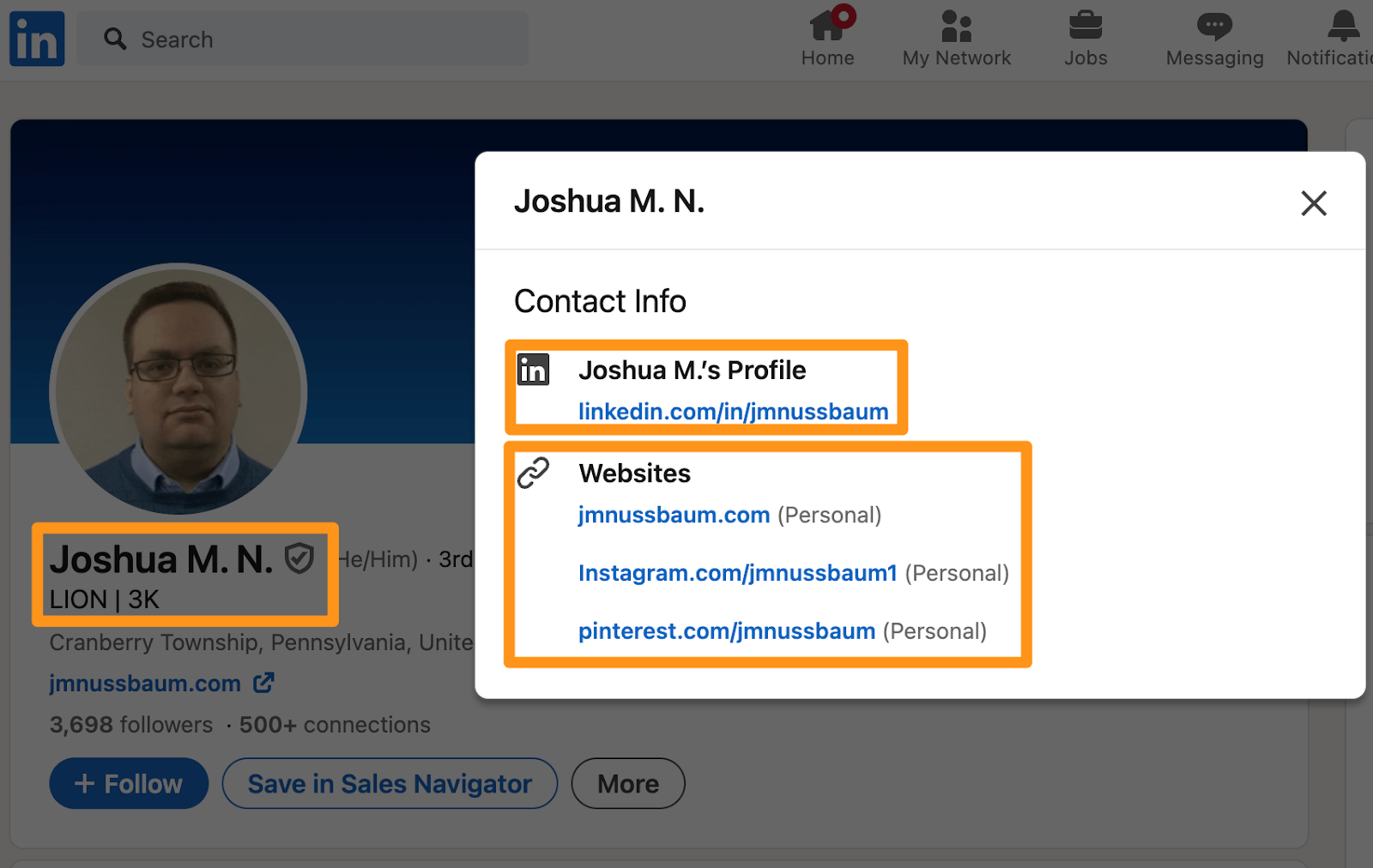
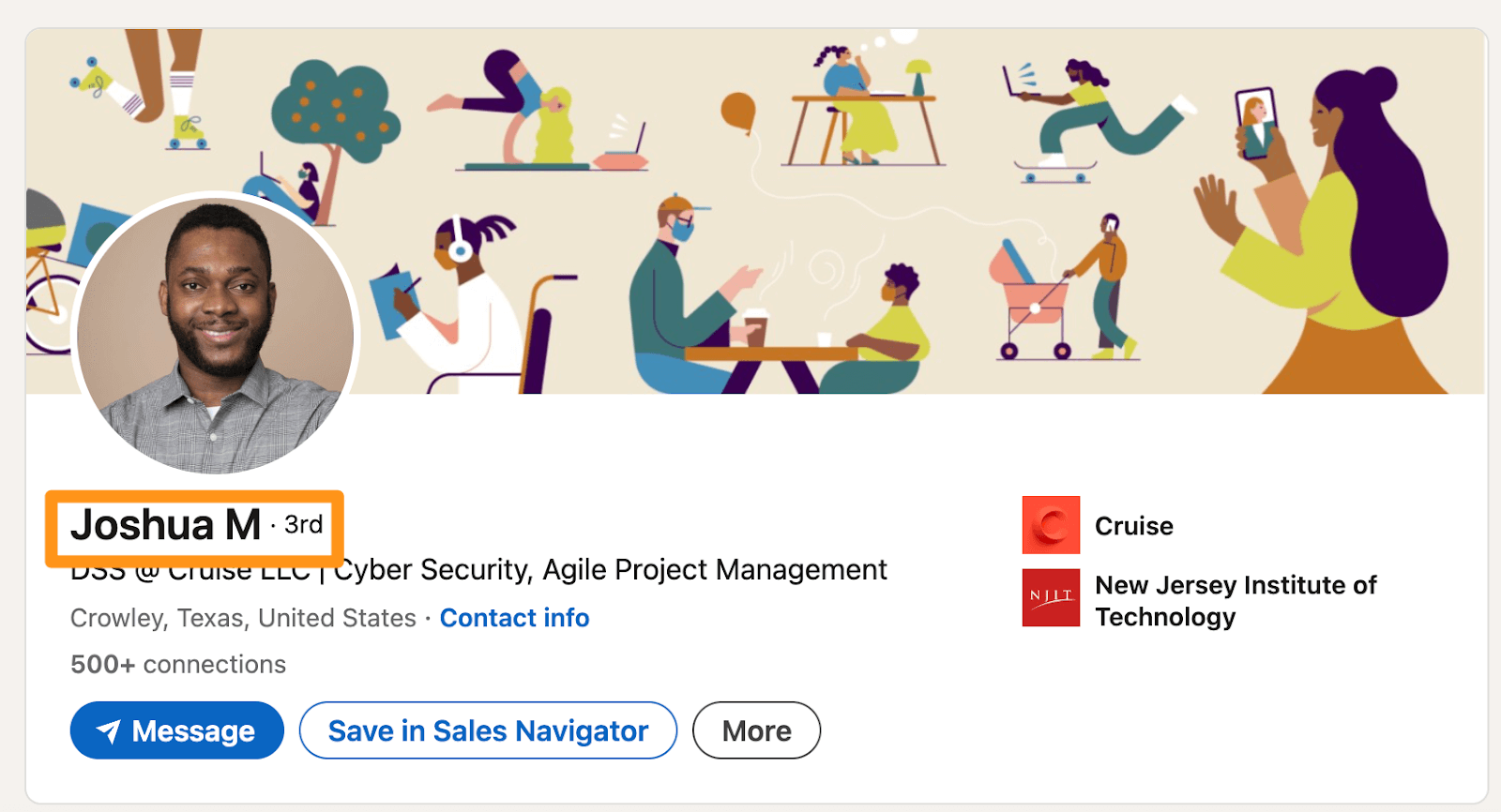
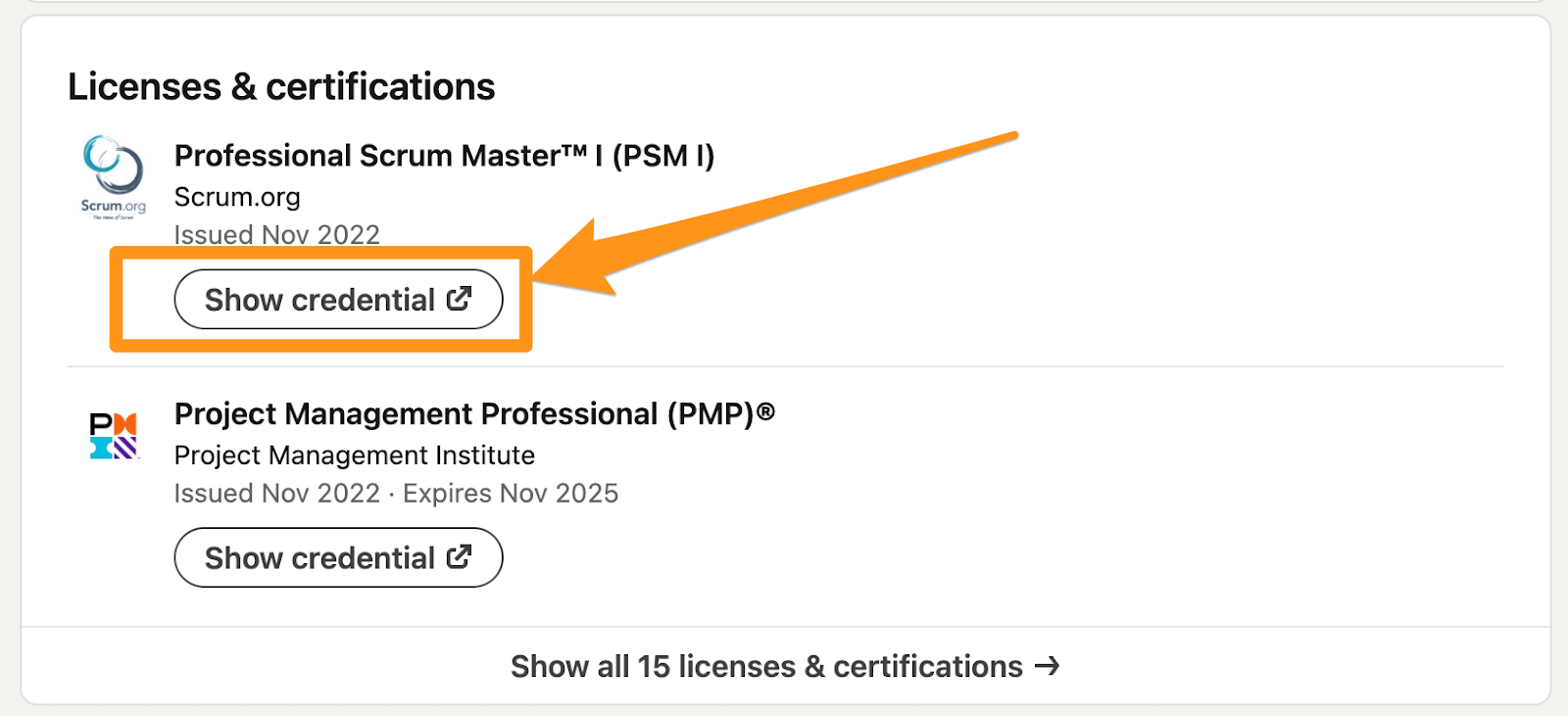
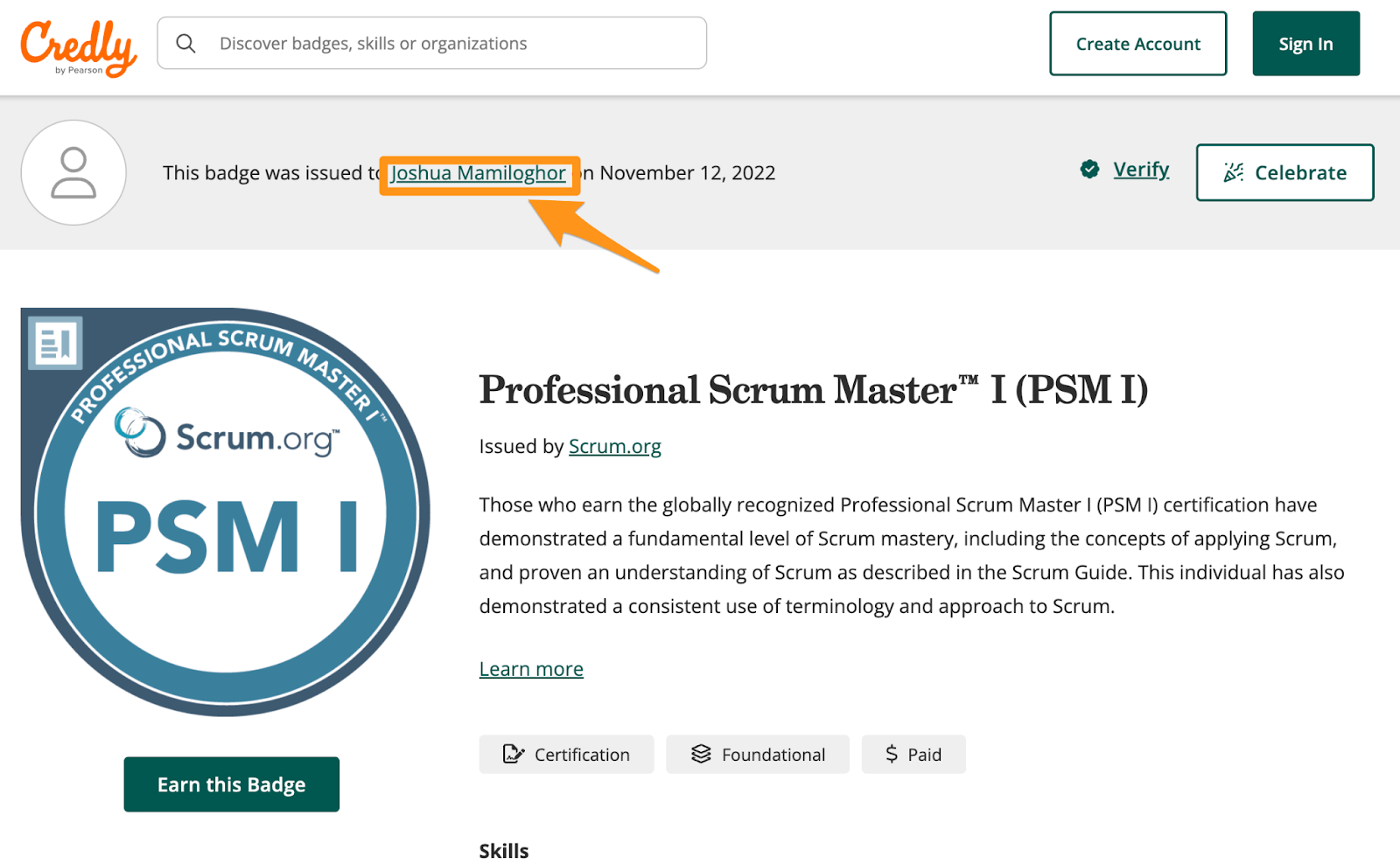
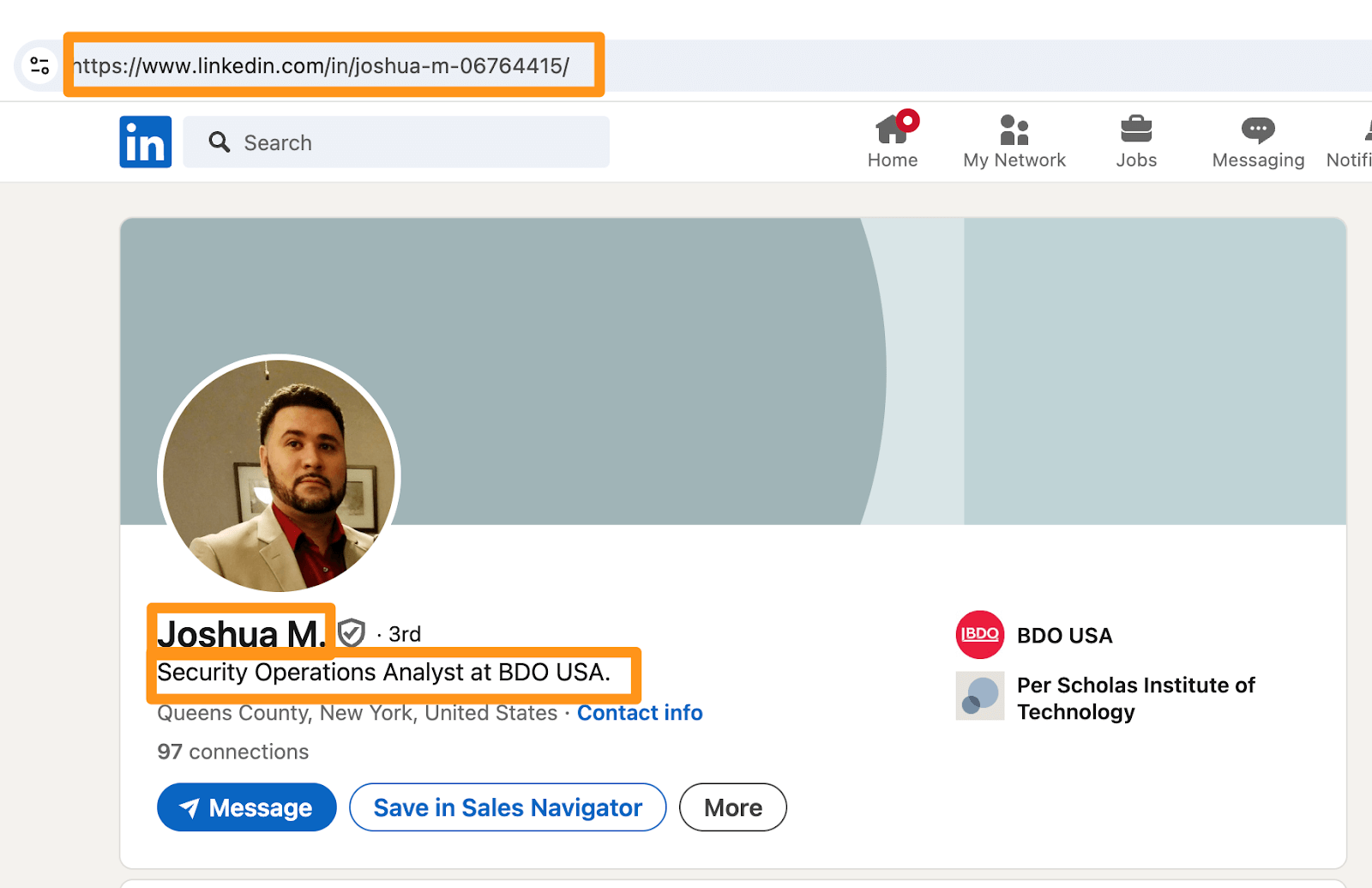
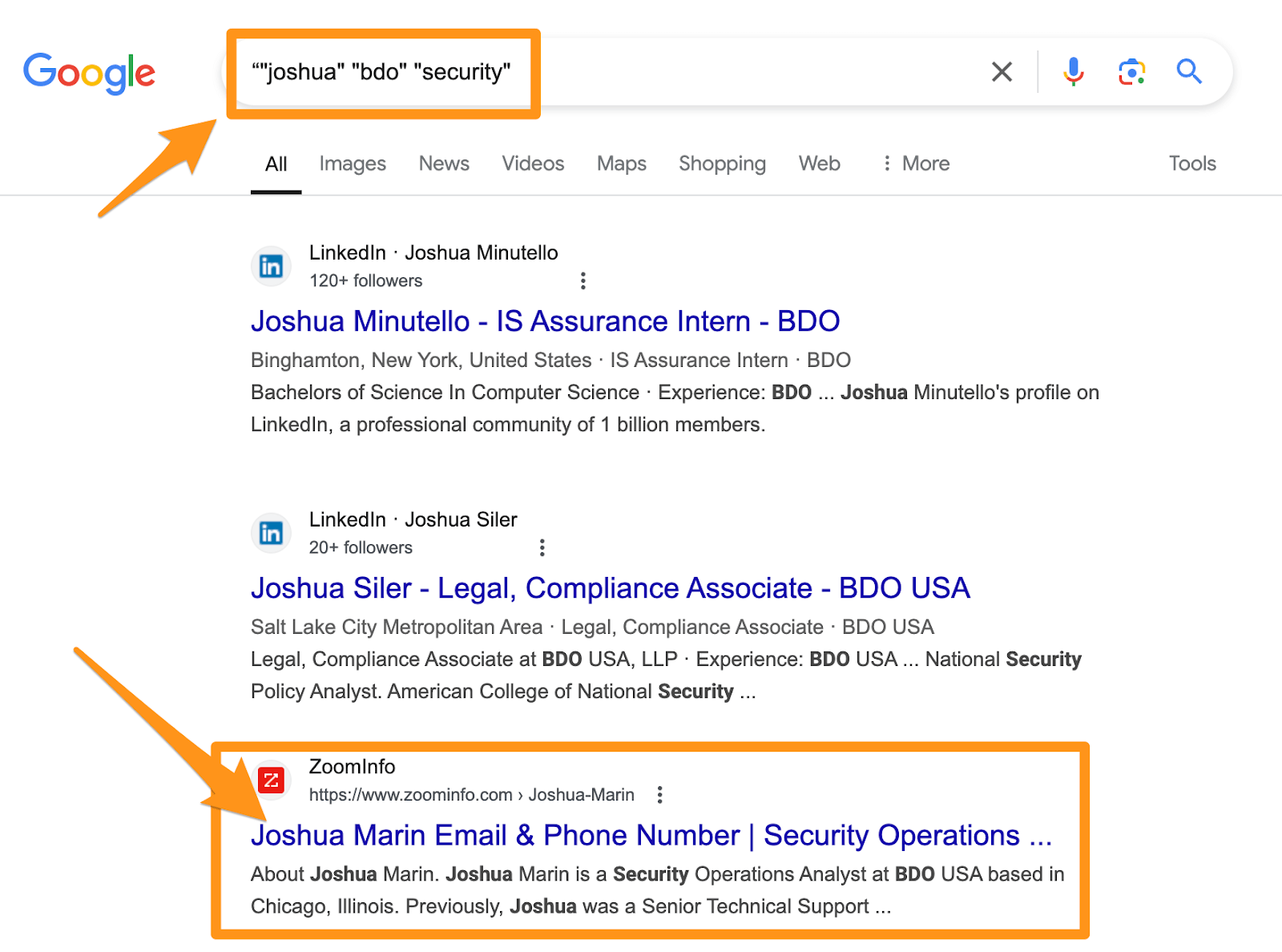
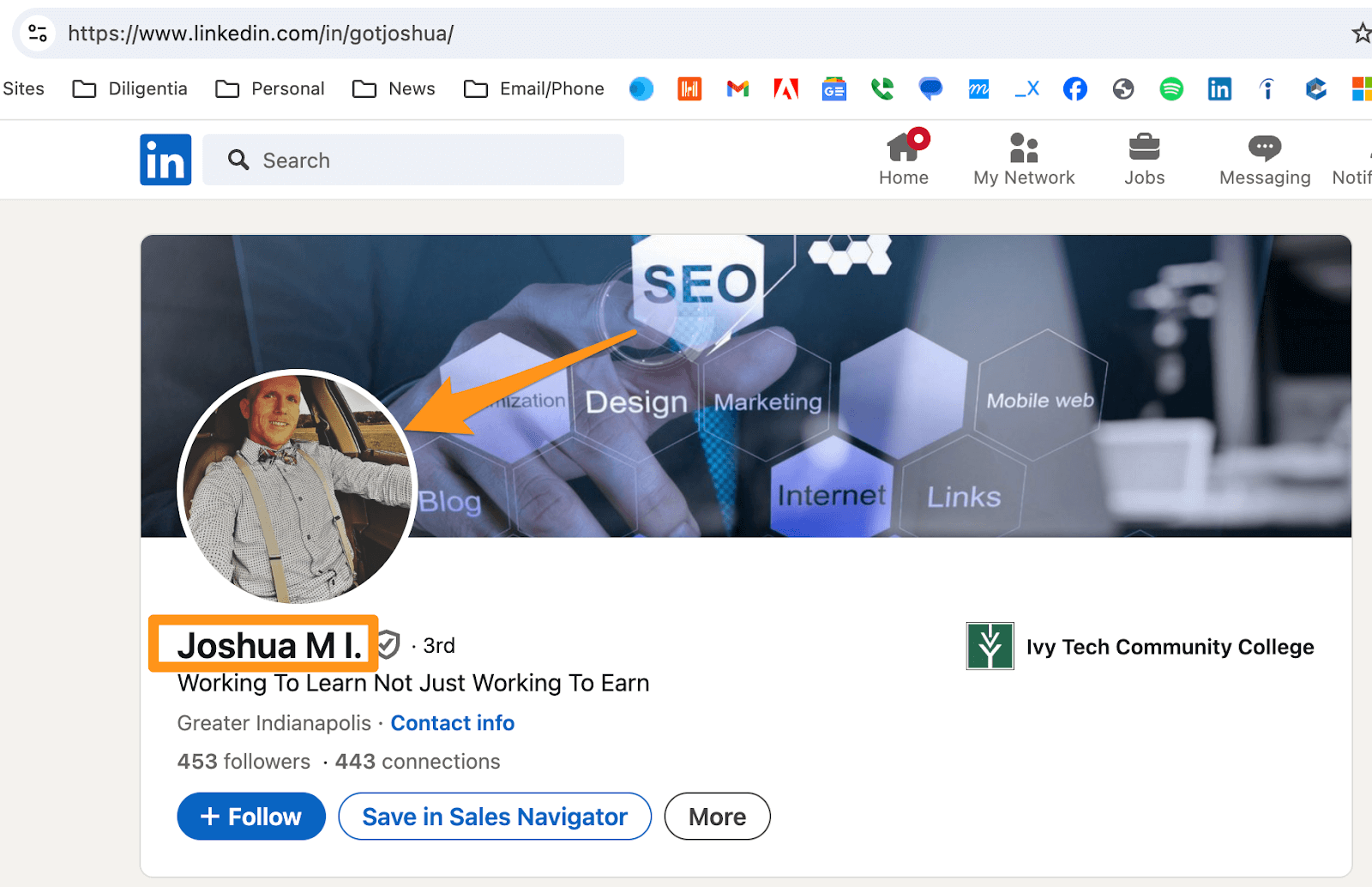
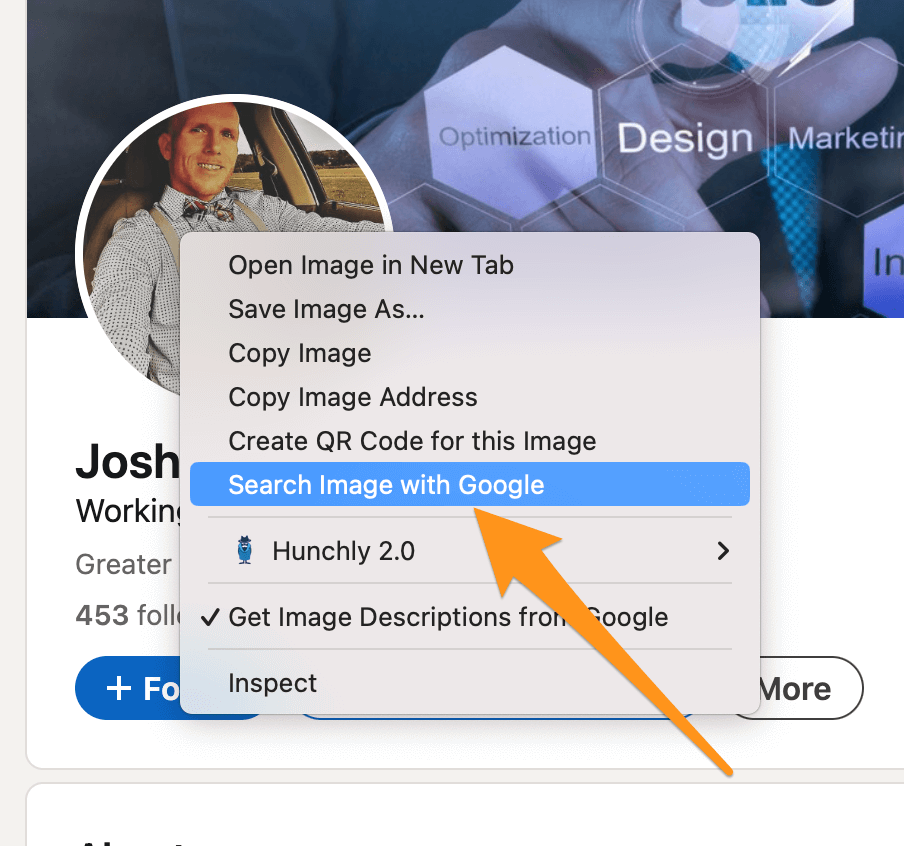
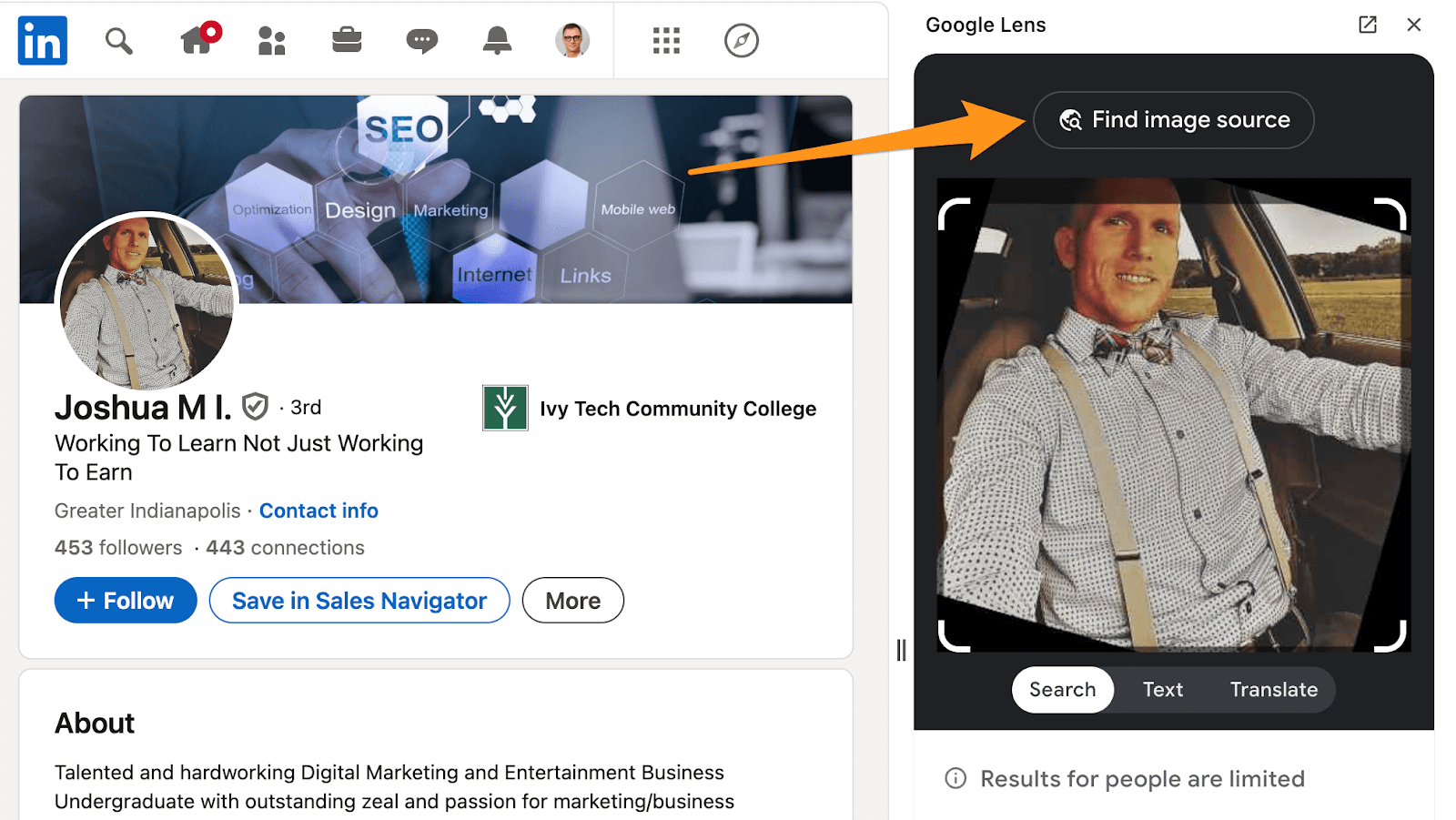
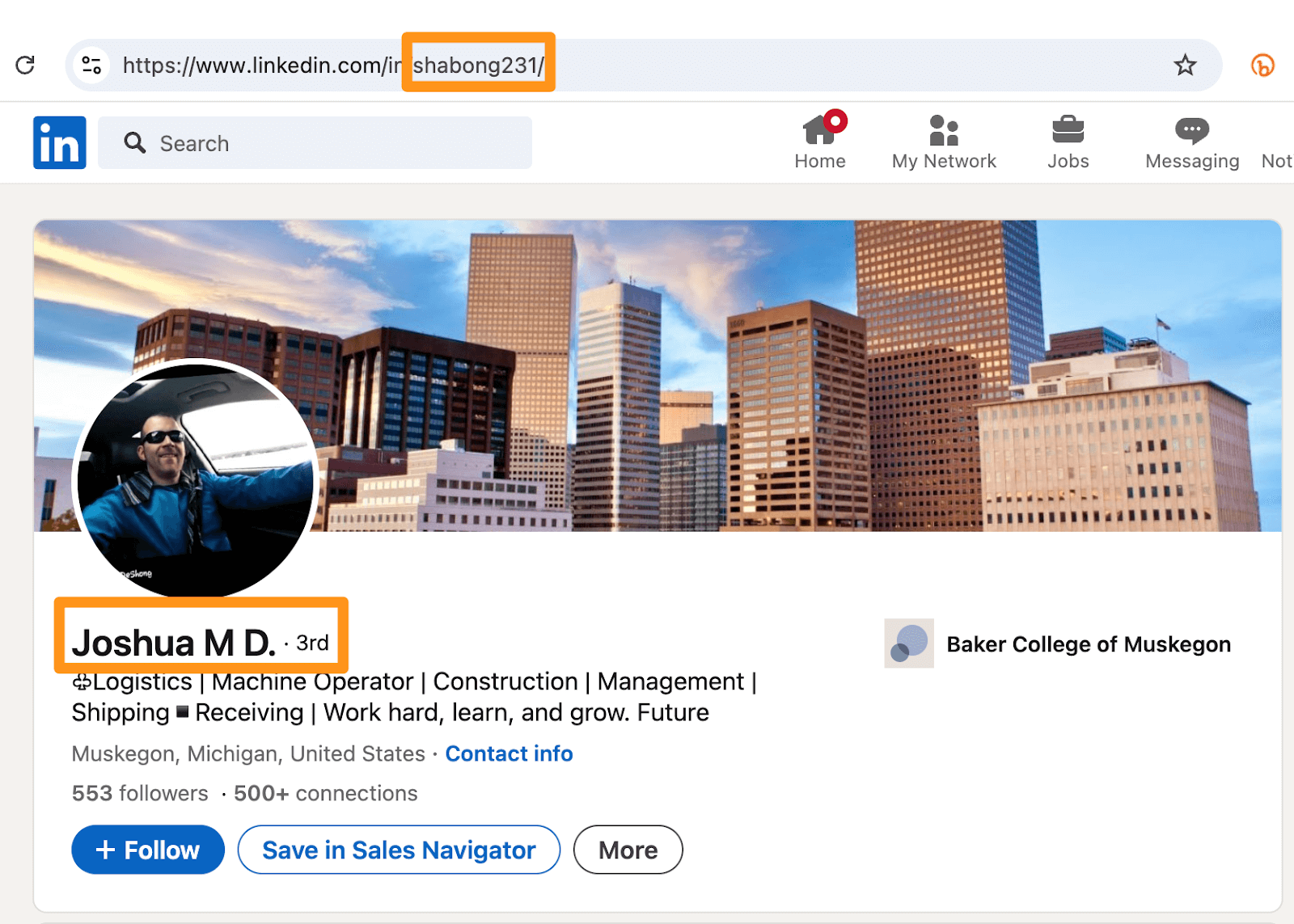
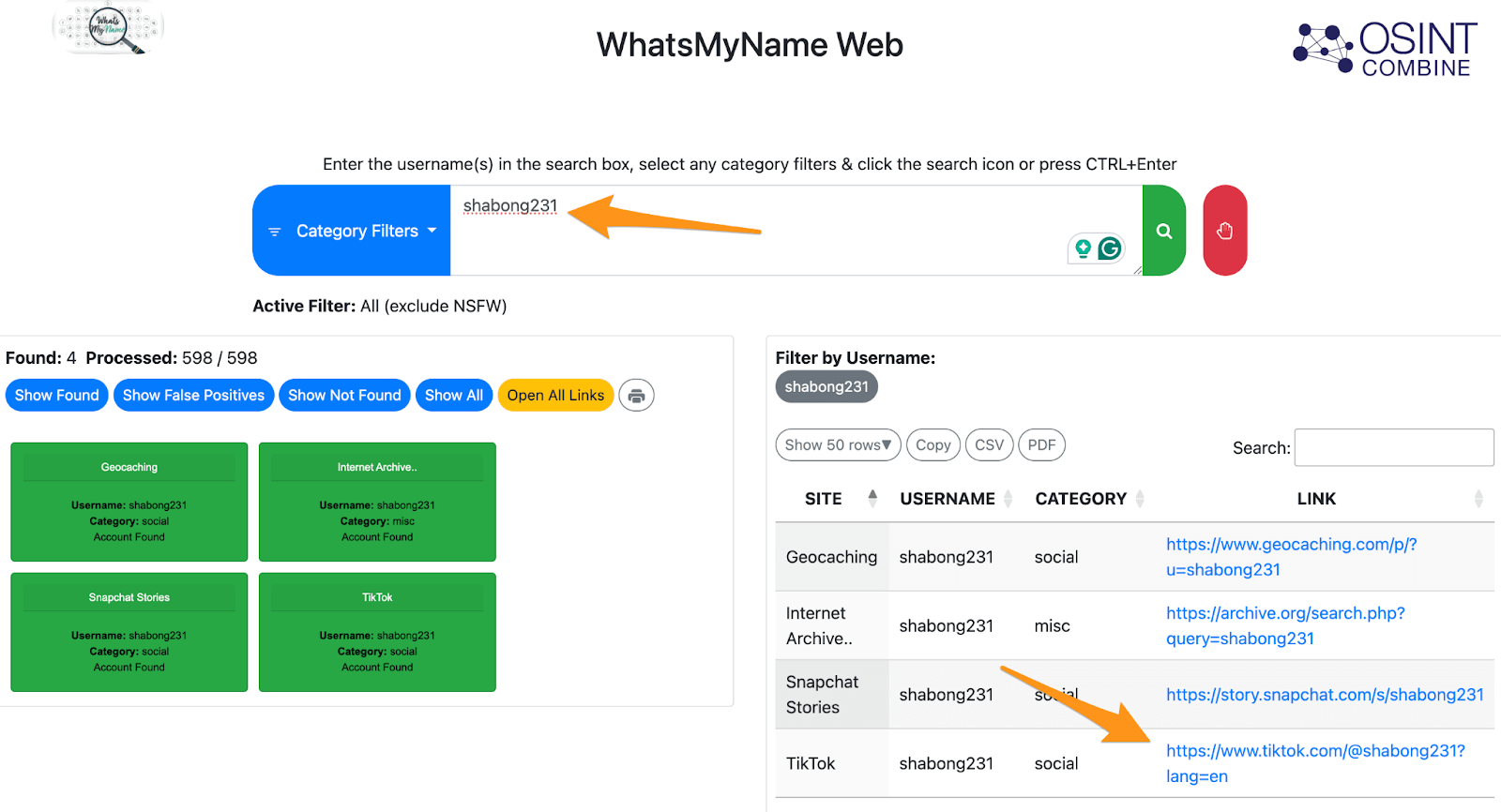
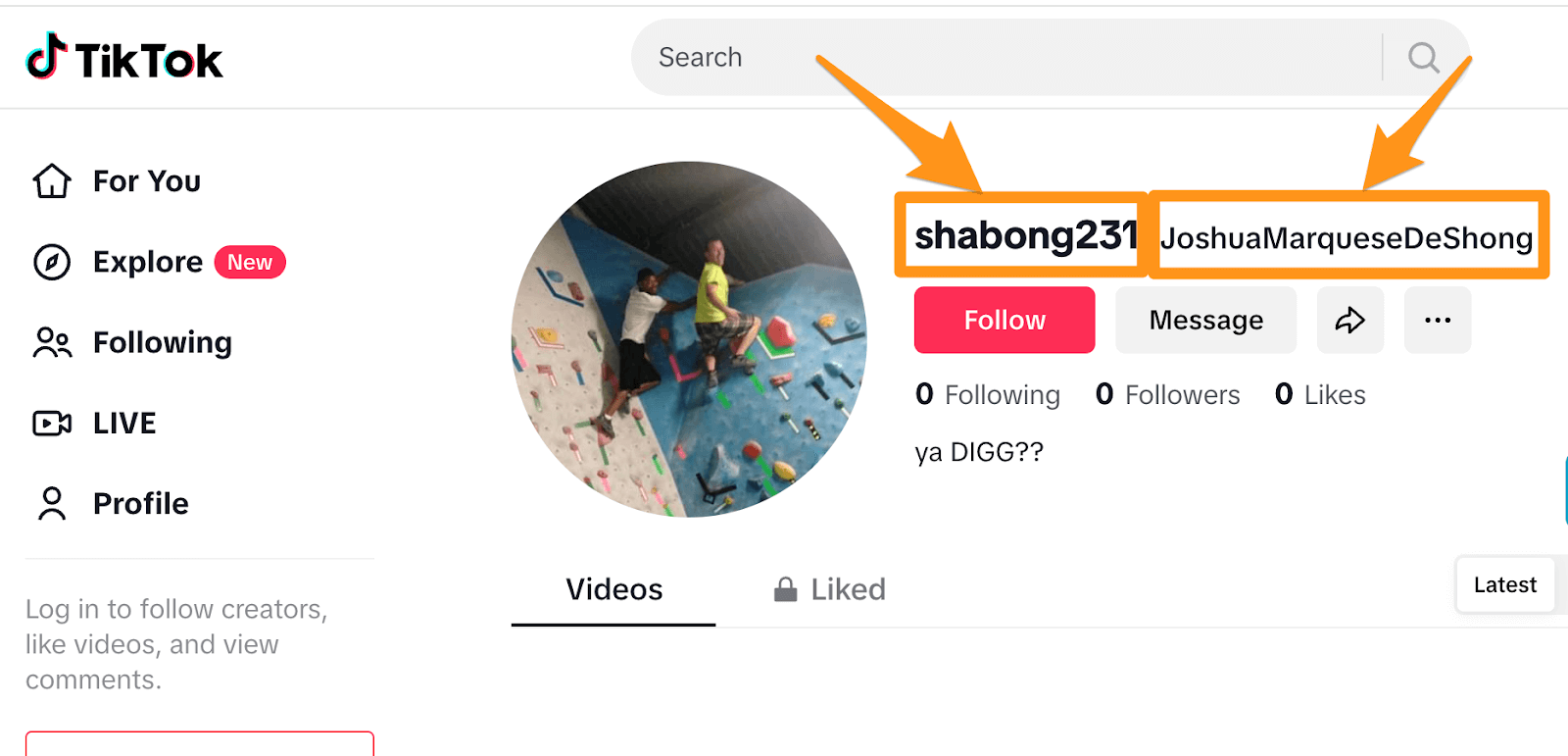
To begin the investigative process, it’s essential to gather all visible information. Key data points include usernames, email addresses, writing styles, images, and posting patterns, as these elements can offer valuable insights. Many individuals often use the same username across different platforms, meaning a handle found on X (formerly known as Twitter) may also be present on Reddit and in various forums or professional profiles. Additionally, while a profile photo might seem generic, utilizing a reverse image search can uncover other locations where the image is used and possibly reveal embedded metadata.
Following Digital Clues: How Anonymous Accounts Leave a Trail
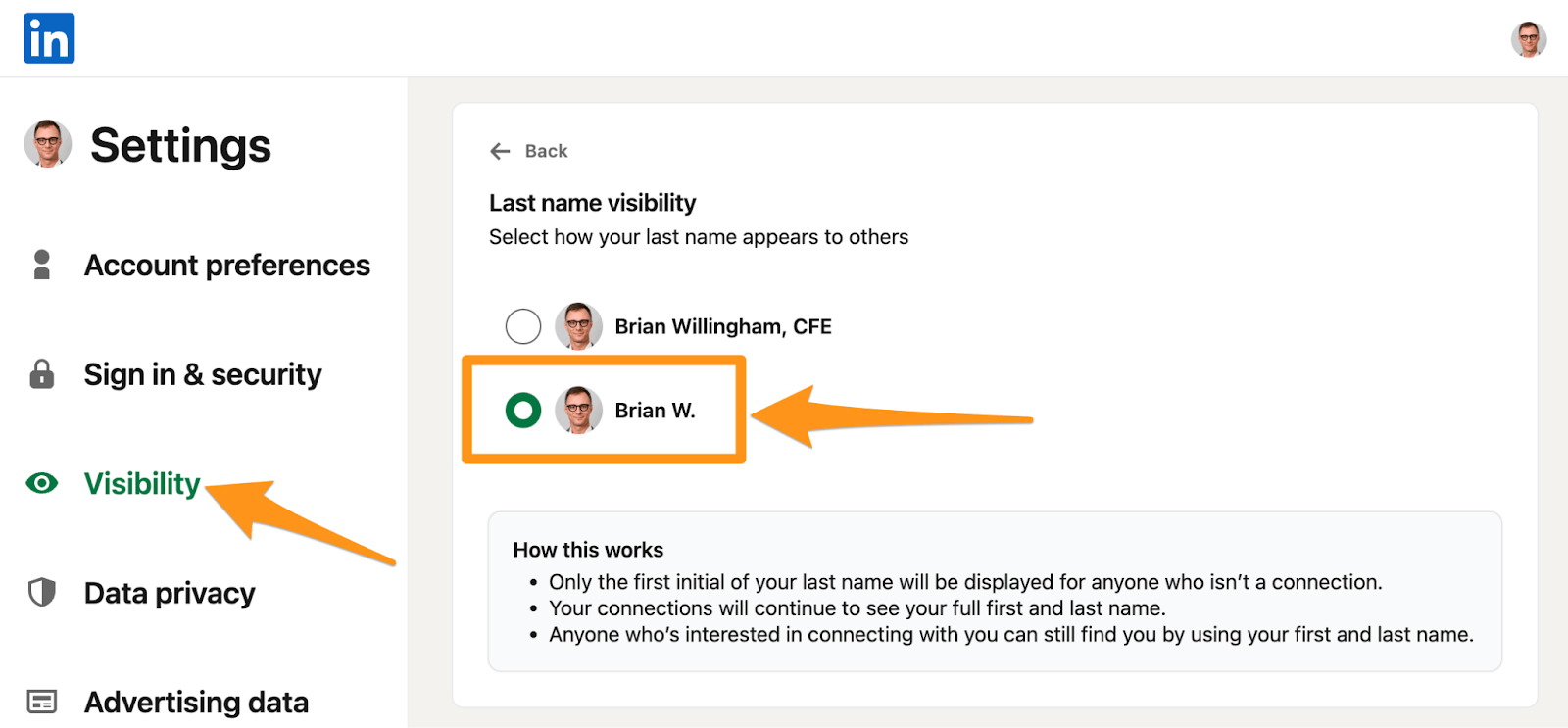
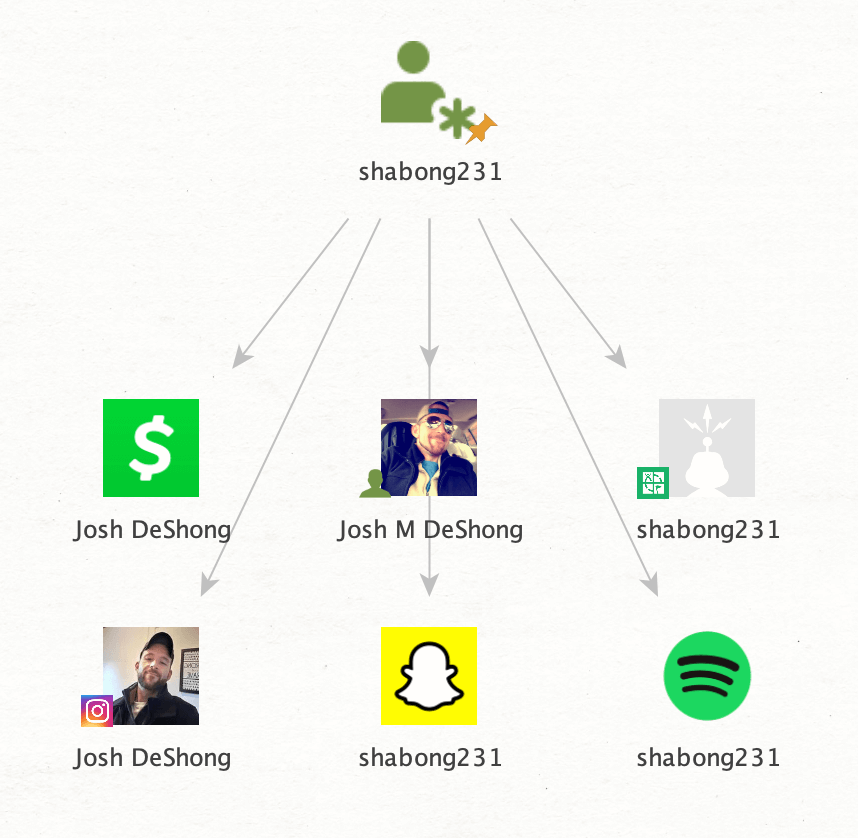
The fun part begins with following the digital footprint. Anonymous individuals often leave small traces behind. These traces might include an email address linked to an abandoned social media profile, a domain registration that hasn’t been fully anonymized, or even a LinkedIn profile that follows a similar naming convention. It may also involve tracing the digital interactions of friends, followers, likes, and comments, gradually piecing together a mosaic that reveals the person behind the screen.
Although each piece of information may seem insignificant on its own, when combined, they start to form a clearer picture of a real person. This process encapsulates the essence of OSINT investigations: uncovering scattered clues and organizing them into a cohesive understanding.
Combining OSINT with Public Records for Legal Proof
What really makes these investigations powerful for attorneys is when OSINT is combined with other public record research. Corporate filings, court dockets, property records, and regulatory documents often link digital breadcrumbs to verifiable personal information. For example, a pseudonym mentioned in litigation records or a business registration that lists a previously hidden email address can make all the difference. Or court filings showing a suspiciously similar incident might uncover new leads. This is where unmasking anonymous accounts shifts from internet sleuthing into evidence that can be used strategically in legal proceedings.
In other cases, a group of suspects may surface, and further investigation into their backgrounds might uncover corroborating details that more clearly identify the true account holder. This might involve an account handle that appears suspiciously similar, a record of disseminating false claims, or previous participation in related legal actions.
Why Human Error Is the Weak Link in Online Anonymity
It’s rarely the tech that cracks an anonymous account. It’s the human behind it.
No matter how careful someone thinks they are, human error is the Achilles’ heel. They reuse a username they once used in a college forum. They post a photo without stripping the metadata. Or they leave a trail in the weirdest places—like a Venmo account with public transactions or a Spotify playlist linked to a real name.
It only takes one slip—or one “cracked window”—and the whole hidden identity can come crashing down.
Real Case Study: The Labor Dispute Leak
A Midwest company was under siege.
Anonymous social media accounts were popping up one after another, with each one taking shots at the business and its leadership. Posts accused the company of corruption, mismanagement, and worse. Employees were rattled. Customers were starting to whisper. And the general counsel knew that if the accusations kept up, it could bleed into the courtroom, the press, or both.
The general counsel’s gut told him it wasn’t random. These weren’t trolls from the outside. This had fingerprints indicating it was an inside job.
At the time, the company was knee-deep in a bitter labor dispute. Tensions were running high. Lawsuits were already in motion. And the general counsel had a list of suspects that was comprised of a smattering of disgruntled employees—about ten in total, each with their own grievances.
That gave us a place to start.
When we began digging, though, the trail was thin. Most of the accounts were locked down, and there were no obvious mistakes or sloppy overlaps. We found just one tiny thread: a partial email address exposed in a past data breach. On its own, it wasn’t much.
But when we lined it up against the suspects, one thing stood out: The partial email, with the exact same unique string of digits, was connected to one of the potential suspects. A coincidence? Not likely.
That was the weak link.
With subpoenas in play, the pressure shifted. The accounts went silent almost overnight. No more anonymous smears. No more burner attacks. Just … nothing.
The message was clear.
The Limitations of Unmasking Anonymous Accounts
It’s important to understand that unmasking anonymous accounts, while often effective, is not a guaranteed process. Some individuals are exceptionally skilled at leveraging practices to ensure digital hygiene. They may use encrypted communications, spoofed IP addresses, privacy-first browsers, burner devices, or offshore hosting services that make tracking extremely difficult. Others may avoid leaving metadata, never reuse usernames, and operate with clockwork-level discipline across platforms.
Even with advanced OSINT tools and experienced investigators, there are cases where the digital trail simply runs cold. Also, legal and ethical constraints limit how far investigations can go in terms of hacking, coercion, and crossing privacy boundaries.
That said, anonymity is inherently fragile. The vast majority of people, even experienced bad actors, make mistakes. They overlook a forgotten account, reuse a unique phrase, or upload an image with embedded data. And in the world of OSINT, it only takes one weak link for an entire hidden identity to unravel.
Patience, persistence, and precision remain the investigator’s most powerful assets. While not foolproof, these methods often succeed where gut instinct and guesswork fail.
Final Takeaway: Anonymity Online Doesn’t Mean They Can’t Be Found
After struggling with online defamation or anonymous harassment, many attorneys find themselves stuck, armed with suspicion but no proof. The internet’s anonymity can make it feel like the truth is out of reach, leaving clients vulnerable and legal options limited.
Now you’ve seen how OSINT and public record analysis can change that supposed anonymity. When it comes to everything from username tracking to digital footprint tracing and metadata analysis, private investigators can bring clarity to otherwise murky digital threats. You’ve also learned how these tools turn loose threads into admissible evidence.
Moving forward, if you’re facing an anonymous attack or suspect digital manipulation tied to a legal matter, don’t wait. Leverage professional OSINT investigation to help you transform suspicion into strategy and protect your clients with facts, not just theories